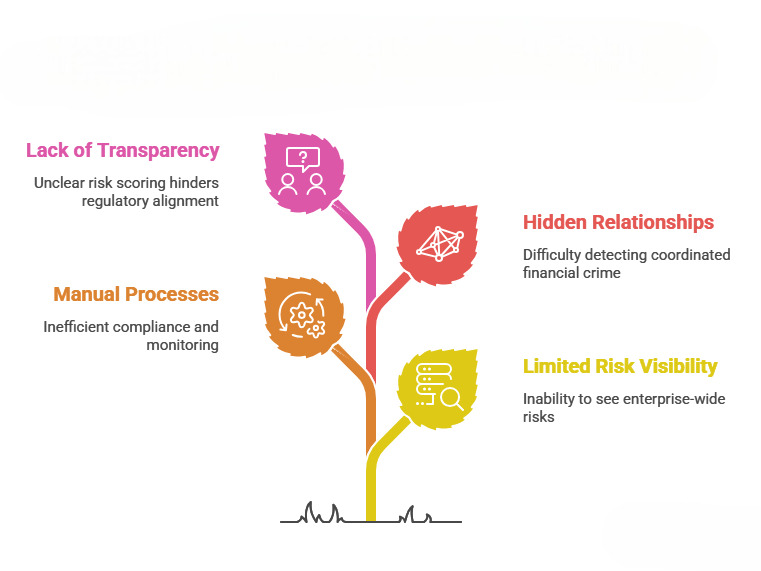
Today’s rapidly evolving digital economy, financial institutions face increasing threats from cybercrime, money laundering, mule networks, identity fraud, insider threats, and sophisticated financial scams. Banks, fintech companies, insurance firms, and payment institutions process millions of real-time transactions across domestic and cross-border channels every day. As digital payments and interconnected financial ecosystems grow, traditional compliance and transaction monitoring systems are no longer sufficient.
Organizations now require intelligent, real-time, and governance-driven risk management systems capable of identifying suspicious behavior before financial losses escalate. One of the most widely adopted governance frameworks for managing operational risk, fraud prevention, and compliance oversight is the Three Lines of Defense (3LOD) model.
While the framework itself remains highly effective, modern financial crime requires these three layers to be strengthened with AI-driven behavioral intelligence, entity-centric monitoring, graph analytics, and explainable risk intelligence.
IDYC360 strengthens all three lines of defense by combining real-time transaction intelligence, entity-centric risk scoring, network analytics, explainable AI, and audit-ready governance capabilities into a unified financial crime risk intelligence platform.
Understanding the Three Lines of Defense
The Three Lines of Defense model helps organizations define clear responsibilities for managing risks, ensuring compliance, and maintaining independent oversight.
The framework consists of:
- First Line of Defense – Operational and business teams responsible for day-to-day risk management.
- Second Line of Defense – Risk management and compliance teams responsible for governance, monitoring, and policy oversight.
- Third Line of Defense – Internal and external audit functions responsible for independent assurance and control validation.
Traditionally, these layers operate independently using fragmented systems and static controls. Modern financial crime environments require these lines to operate through integrated real-time intelligence.
IDYC360 in the First Line of Defense
The First Line of Defense focuses on operational risk management during daily business activities such as customer onboarding, transaction processing, payment approvals, and AML monitoring.
IDYC360 strengthens the First Line through:
- Real-time transaction monitoring and behavioral analytics
- Entity-centric risk scoring across customers, beneficiaries, and counterparties
- Detection of suspicious onboarding behavior and synthetic identities
- Mule account detection and linked entity analysis
- Cross-border payment anomaly detection
- Dynamic sanctions and AML monitoring
- Real-time fraud scoring with explainable alerts
- Monitoring of transaction velocity, geographic drift, and behavioral deviations
Instead of relying only on static rules and thresholds, IDYC360 continuously evaluates behavioral patterns and network relationships to identify emerging risks early during daily operations.
This enables operational teams to move from reactive monitoring to proactive fraud prevention.
IDYC360 in the Second Line of Defense
The Second Line of Defense focuses on enterprise-wide risk governance, compliance oversight, regulatory alignment, and policy management.
IDYC360 enhances the Second Line through:
- Enterprise-wide risk visibility and centralized monitoring
- AI-driven behavioral and entity-based risk scoring
- Graph intelligence for fraud ecosystem detection
- Cross-border payment and AML/CTF risk monitoring
- Explainable AI for governance and regulatory transparency
- Automated compliance alerting and escalation workflows
- Continuous monitoring of evolving fraud typologies
- Regulatory-ready risk intelligence dashboards
Modern financial crime often involves coordinated networks, structured transaction flows, and hidden relationships between accounts. IDYC360’s graph and network intelligence capabilities help compliance teams detect fraud ecosystems rather than isolated suspicious transactions.
The platform also supports governance-led AI adoption by providing transparent and explainable risk scoring aligned with regulatory expectations.
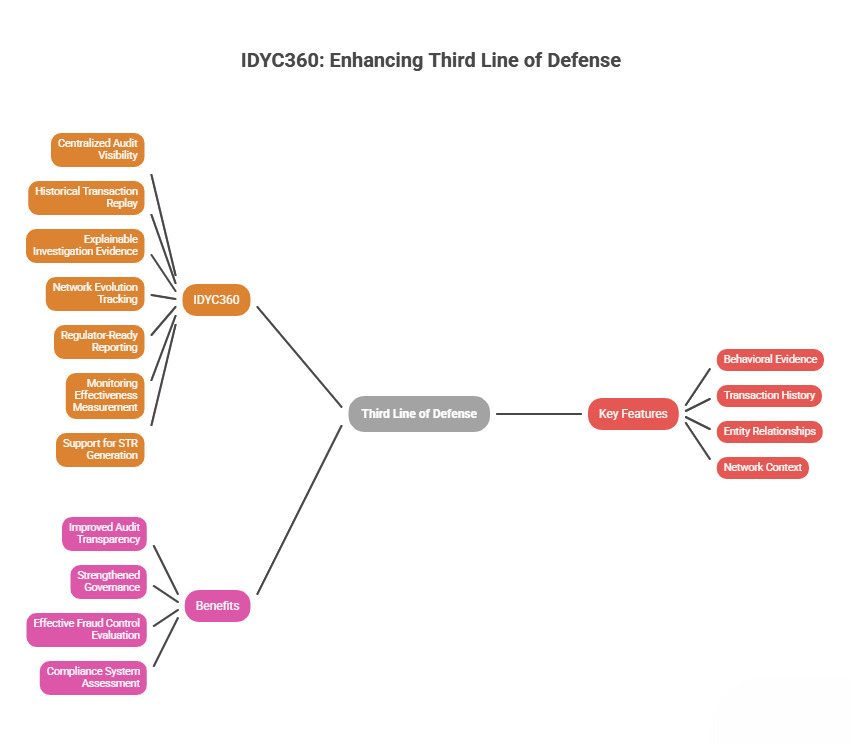
IDYC360 in the Third Line of Defense
The Third Line of Defense provides independent oversight, audit assurance, and evaluation of the effectiveness of organizational controls.
IDYC360 strengthens the Third Line through:
- Centralized audit visibility and investigation traceability
- Historical transaction replay and forensic analysis
- Explainable investigation evidence and risk rationale
- Network evolution tracking and behavioral history analysis
- Regulator-ready reporting and audit support
- Monitoring effectiveness measurement and governance reporting
- Support for STR generation and compliance investigations
Every decision and alert generated within IDYC360 can be traced with supporting behavioral evidence, transaction history, entity relationships, and network context.
This improves audit transparency, strengthens governance, and enables independent reviewers to evaluate how effectively fraud controls and compliance systems are operating.
Example Scenario
Suppose fraudsters attempt to create multiple fake accounts using linked devices, synthetic identities, and structured transaction networks across multiple payment channels.
In this scenario:
- The First Line of Defense detects suspicious onboarding behavior, abnormal transaction velocity, and unusual payment activity in real time.
- The Second Line of Defense identifies linked entities, network risk propagation, coordinated behavior patterns, and cross-border anomalies using graph analytics and AI-driven intelligence.
- The Third Line of Defense independently validates whether monitoring controls, risk escalation processes, and investigation procedures worked effectively and complied with governance expectations.
By combining behavioral intelligence, graph analytics, and explainable AI, IDYC360 enables organizations to detect suspicious activities earlier, reduce false positives, improve investigation quality, and strengthen operational resilience.
Strategic Benefits of IDYC360
Organizations implementing intelligent risk intelligence platforms gain several strategic advantages:
- Faster fraud detection and response
- Reduced false positives and alert fatigue
- Improved AML/CFT compliance monitoring
- Enhanced cross-border transaction visibility
- Stronger audit and investigation transparency
- Governance-led AI oversight
- Real-time entity and network intelligence
- Improved operational resilience and customer trust
IDYC360 transforms fraud prevention from reactive investigation into predictive and intelligence-driven risk containment.
Conclusion
The Three Lines of Defense model remains one of the most important frameworks for managing operational risk, preventing fraud, and strengthening compliance within financial institutions.
However, modern financial crime requires more than static controls and fragmented monitoring systems. Institutions need intelligent platforms capable of operating in real time, understanding entity behavior, identifying hidden relationships, and generating explainable governance insights.
IDYC360 strengthens all three lines of defense by integrating:
- Real-time behavioral analytics
- Entity-centric intelligence
- AI-driven fraud detection
- Graph and network risk analysis
- Continuous compliance monitoring
- Audit-ready transparency
As financial institutions continue facing growing cyber threats, digital fraud, regulatory pressure, and cross-border financial risks, intelligent risk infrastructure will become foundational to long-term trust, resilience, and governance.
Frequently Asked Questions
Q1. What is the Three Lines of Defense model?
The Three Lines of Defense is a governance and risk management framework used to strengthen operational controls, compliance oversight, and independent audit assurance.
Q2. Why is the Three Lines of Defense important?
It helps organizations reduce fraud risks, strengthen compliance, improve governance, and protect financial systems from operational and regulatory failures.
Q3. How does IDYC360 strengthen the First Line of Defense?
IDYC360 strengthens the first line through real-time transaction monitoring, behavioral analytics, entity-centric intelligence, and fraud detection capabilities.
Q4. How does IDYC360 support compliance and governance teams?
It provides enterprise-wide risk visibility, AI-driven monitoring, explainable risk intelligence, graph analytics, and automated compliance workflows.
Q5. How does IDYC360 improve audit and investigation processes?
It provides audit-ready traceability, historical transaction analysis, explainable investigation evidence, and regulator-ready reporting capabilities.
Ready to Stay
Compliant—Without Slowing Down?
Move at crypto speed without losing sight of your regulatory obligations.
With IDYC360, you can scale securely, onboard instantly, and monitor risk in real time—without the friction.